Cybersecurity Course
Worried about falling behind in the competitive job market? Gain the skills to detect threats, protect critical systems, and build a career in a high-demand field with practical Cyber security training.
Pay little or no cash with government subsidies:

Our Cybersecurity course alumni come from industry-leading organisations


Learn Cybersecurity with Vertical Institute
Who is This Course For
All Professionals
Enhance your Cybersecurity skills with the latest tools to protect data and systems.
Aspiring Cybersecurity Professionals
Kickstart your career in Cybersecurity with no prior experience necessary. Transform your curiosity into expertise and open the doors to a thriving industry.
Entrepreneurs and Business Owners
Safeguard your business by understanding Cybersecurity threats and solutions. Make informed decisions to protect your assets and reputation.
Students and Lifelong Learners
Whether you’re a student or a lifelong learner, acquire this in-demand skill set that is crucial in today’s data-driven world.
Skills You’ll Learn
Cybersecurity Course Details
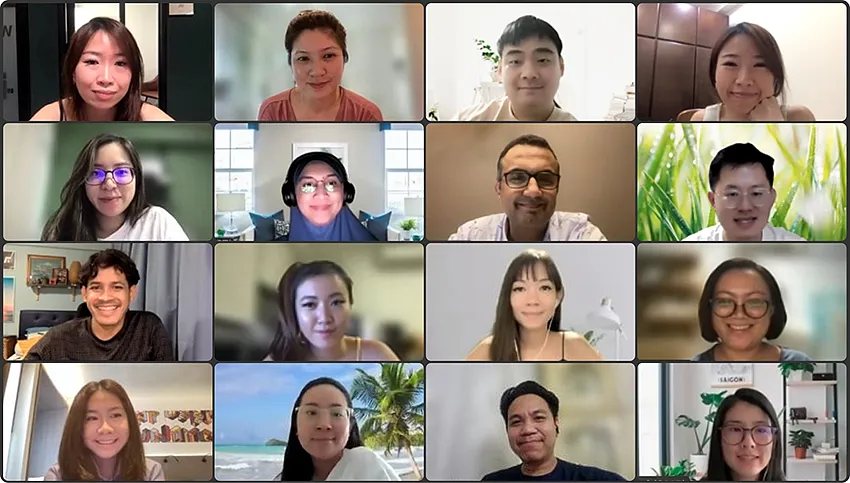
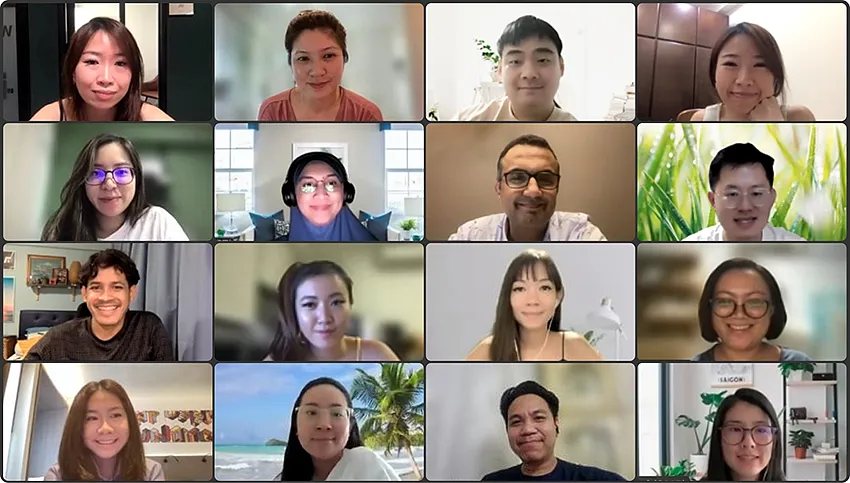
Online classes via Zoom
7 Lessons, 3 hours each session
1 Instructor + TA supports
Course Fee & Government Subsidies
Pay even less or 0 cash with government subsidies
Singaporeans aged 40 and above
Singaporeans aged below 40
Permanent Residents
- SFC: All Singaporeans aged 25 years old and above can use SkillsFuture Credits to fully offset the remaining fees.
- UTAP: In addition, NTUC members can utilize UTAP to offset 50% of remaining fees (capped up to $500 per year).
Have questions? Read FAQs or Contact Us.
Detailed Cybersecurity Course Curriculum
Master the fundamentals of Cybersecurity through our comprehensive and hands-on curriculum.
Pre-Work
As a VI student, you will be given access to online learning materials in our e-learning portal.
To get you ready for learning, this essential pre-work will familiarise you with the basics of the key concepts and tools we will be using throughout the course.
Although you will learn these topics remotely before you arrive in class, you won’t be far away from the resources of the VI community. Make use of our Telegram channel to leverage connections with students, alumni, instructors and experts. At the end of your pre-work, you’ll be ready for the fast pace on campus!
After the course, you can choose to participate in follow-up sessions with your instructor, either in a group and/or individually, included as part of the course fee.
Module 1: Introduction to Cyber Security
Tutorials:
- Internet, sea of opportunities and threats
- Types of cyber criminals
- Cybersecurity goals of Confidentiality, Integrity, and Availability
- Types of cyber-attacks
- Security trends in Singapore and across the globe
- Example of Open-Source Intelligence attack
- Introduce OpenAI for brainstorming case studies and generating detailed explanations of security incidents
Activity:
- Check on account exposure
- Case study on cybersecurity goals on organisations
- Review on recent security incidents affecting organisations in Singapore and map to cybersecurity goals
- Introduce the capstone project to students
Module 2: Cyber-Attack Chain
- Cyber-security snapshot
- Cyber-Attack chain
- Reconnaissance
- Weaponisation
- Delivery
- Exploitation
- Installation
- Command and Control
- Actions on Objective
- Security technologies
- Anti-virus
- Security monitoring
- Intrusion detection and prevention systems
- Identity and access management
- Biometrics
- Security scanners
- Security controls
- Demonstration of hacking examples mapped to the Cyber-Attack Chain phases
- Threat Modeling against organisation
Activity:
- Map security controls against cyber-attack chain
- Threat modeling
- Let’s rob a bank hacker simulation
Module 3: Online Security
Tutorials:
- Password security
- Brute-force attacks
- Commonly used passwords
- Previously exposed passwords
- Password strength
- Multi-Factor Authentication
- Account security
- Email accounts
- Social media accounts
- Bank accounts
- Open-Source Intelligence (OSINT)
- Phishing
- Scams type related to organisations
- Fake bank’s website
- SMS verification
Activity:
- Password strength checker
- Enable multi-factor authentication in accounts
- Adjust privacy settings for social media accounts
- Check for activities online of accounts
- Search for information of a company using Open-Source Intelligence
Module 4: Risk Management - Perimeter of Exposure
Tutorials:
- Cybersecurity risks examples to organisations
- Security risks and recommendations relating to
- Wireless
- Mobile
- Laptop
- USB device
- Web cameras
- Risk management
- Importance of Cybersecurity Risk Assessment
- Risk identification
- Examples
- Risk analysis
- Risk evaluation
- Guidelines on Risk Management Practises – Internet Controls for organisations in Singapore
- Vendors’ risk management
- Service providers’ risk management
- Insider threats’ risk management
Activity:
- Check for shared folders in computer
- Check for mobile application permission settings
- Update computers and mobile devices
- Enable antivirus and firewall on computers
- Determine cyber risks and responses for an organisation
Module 5: Social Engineering
- Tactics and techniques of social engineering
- Key principles with examples on organisations
- Authority
- Intimidation
- Social proof
- Scarcity
- Urgency
- Familiarity
- Social engineering vectors
- Vishing
- Phishing
- Smishing
- Impersonation
- Distinguish between a real and a scam email
- Distinguish between a real and a phishing website
- The Dark Web
Activity:
- Review third-party access to accounts
- Set browser security
- Design security program to prevent social engineering attacks
Module 6: Cybersecurity Regulations
- Personal Data Protection Act (PDPA)
- Objectives of securing our personal data
- How PDPA works
- Applying PDPA to personal and work activities
- Protecting personal data online
- MAS TRM
- Establish Sound and Robust Technology Risk Governance and Oversight
- Maintain Cyber Resilience
Activity:
- Case study on commission decisions
Module 7: Incident Preparedness and Response
- Why prepare for incidents?
- Assumed breach mindset
- Incident preparedness and response in organisation
- Preparation
- Detection and analysis
- Containment and eradication
- Post-incident recovery
- Incident response checklist
- Cyber-Security career tracks
Activity:
- Incident response simulation
- Capstone project discussion
The Capstone Project
Participants will be required to identify cyber-security issues facing companies in Singapore, and to provide security recommendations against this issue based on recent security trends in Singapore.
The capstone project will culminate your learning by applying the security policies, awareness and technology learnt into a stakeholder presentation that includes:
- Addressing real-world security cases in Singapore
- Identify risks to a organization
- Introduce security controls to address the identified risks
Upcoming Cybersecurity Course Schedules
Meet our Instructors

Liangyang
Principal Security Specialist Technical Account Manager @ (AWS)
Bachelor’s of Computing in Information SystemNational University of Singapore


George
Senior Manager, CloudSec & AppSec @ Dyson
Master of Computing (Infocomm Security), NUSBachelor of Science (Information Systems), SMU

Peter
CO-Founder, CEO @ Synectify
Dr of Philosophy, National University of Singapore


Anthony
IBF TFIP Cybersecurity Instructor
Bachelor’s in Information Technology University of Wollongong

How to Apply in 3 Simple Steps
Select Class Schedule (1/3)
Choose convenient classes on evenings or weekends.
Calculate Your Subsidies (2/3)
Fill out the form to calculate your government subsidies.
Confirm Your Spot With Just $100 (3/3)
Instead of paying the full fee, place a small deposit to secure your slot.
8 Reasons to Learn Cyber Security with Vertical Institute

Beginner-Friendly
Upskill with our Cybersecurity even with no prior background or experience.
Professional Certificate
Gain an accredited and recognised course certification in Singapore.
Expert-led Learning
Learn concepts and tools through expert-led lectures, discussions and project work.
Hands-on Training
Full hands-on training using industry tools in real-life scenarios.
Out of Class Support
Get out of class supports from teaching assistants and instructor.
Lifetime Resource Access
Unlock lifelong learning with access to course materials and support.
Community Benefits
Be part of the VI community and leverage connections with alumni and experts.
Career Support
Dedicated career support and job matching with hiring partners.
30,000+
Alumni graduated
#1
Most reviewed
4.9 / 5
Overall rating
100+
Hiring partners
Get Certified in Cybersecurity in Just 21 Hours

Upon successful completion of this IBF-accredited course, you will be awarded a cybersecurity certification recognised by employers in Singapore. VI alumni can use their course certificate to demonstrate skills to employers and their network.
Pro Tips💡: Show your certification on LinkedIn to enhance your professional image and attract potential employers.
Job Placement Assistance
Vertical Institute offers Job Placement Assistance to graduates that have successfully completed any of our courses.
Over 100 hiring partners
Land internship & industry opportunities
Apply your new skills learnt
What Our Students Say About the Cybersecurity Certification?

Kyaw T.
Cybersecurity Alumni
In the ever changing world with technology, there will always be a threat to cybersecurity. Expert instructor at Vertical Institute covered key concepts like network security, ethical hacking, and incident response which allows me to take the first step in cybersecurity and definitely would like to explore more opportunities in this expertise.

Calvin Tan
Cybersecurity Alumni
I'm grateful for the guidance and mentorship of LOI LiangYang, course instructors from AWS, who have been awesome in guiding us to a better understanding of Cybersecurity best practices and industry trends. This experience has not only broadened my technical capabilities but also deepened my commitment to ensure we secure our own digital environment.
Thank you Vertical Institute for this incredible learning journey!!! Thank you to the awesome Admins of VI, and also to the learners.

Guan Jie Lim
Cybersecurity Alumni
Thank you to Vertical Institute for curating a practical and useful curriculum! I have thoroughly enjoyed this course and look forward to learning more and further expanding my knowledge regarding Cybersecurity!
FAQs About the Cybersecurity Course
What is Cybersecurity?
“Recruitment firm Michael Page is seeing growing demand for cyber-security positions such as security operations manager and IT risk manager. Salaries for these roles can range from $10,000 to $12,000 a month, said Michael Page Singapore recruiter Isha Hussain.”
– The Straits Times, 1 May 2022
As our daily lives become increasingly dependent on internet-based tools and services, such platforms begin to amass more of our sensitive data.
Coupled with the ever-evolving cyberattacks and increasing creativity from hackers today, it continues to leave our computer systems and IoT in a vulnerable state. However, by utilising cybersecurity, it can help to prevent cyberattacks, data breaches, identity theft, and aid in risk management.
Are there course fee subsidies available?
The IBF Standards Training Scheme (“IBF-STS”) provides funding for training and assessment programmes accredited under the Skills Framework for Financial Services.
For our training programmes that are IBF-accredited, eligible Singaporeans & PRs may receive funding support under the IBF Standards Training Scheme (IBF-STS), subjected to all eligibility criteria being met.
For more information on the funding support, please visit: https://www.ibf.org.sg/programmes/Pages/IBF-STS.aspx
Can I use SkillsFuture Credits to pay for the remaining course fee after funding?
To check your SkillsFuture credit balance, please follow these steps:
- Go to https://myskillsfuture.gov.sg
- Click on ‘Submit SkillsFuture Credit Claims’
- Login with your SingPass
- Click on the arrow (>) at the top right hand corner. You will be able to see a drop-down list of your Available SkillsFuture Credits.
After you have registered for a course, a VI representative will reach out to guide you with the SkillsFuture Credits
*Please note that our courses are not eligible for “Additional SkillsFuture Credit (Mid-Career Support)’. You will only be able to use available credits from ‘SkillsFuture Credit’ and ‘One-off SkillsFuture Credit Top-Up’.
Can NTUC Union members use UTAP to offset the remaining course fee after funding?
Yes, all our courses are eligible for Union Training Assistance Programme (UTAP) Funding. NTUC Union members can use UTAP to offset 50% of unfunded course fees (capped at $500 per year).
This claim must be done after completion of the course. Please refer to the UTAP FAQ for more information.
Can I use SkillsFuture Credits and UTAP at the same time?
For illustration purposes only:
Who is eligible for IBF funding support?
All Singaporeans or Singapore Permanent Residents (PRs) that are physically based in Singapore and successfully complete the course will be eligible.
- Be a Singaporean Citizen or PR physically based in Singapore
- Minimum of 75% attendance (this means that you must attend at least 6 out of 7 lessons)
- Pass the assessment
For Company-Sponsored:
- Be from Financial Institutions that are regulated by the Monetary Authority of Singapore (MAS) (either licensed / exempted from licensing) or Fintech companies that are registered with the Singapore Fintech Association.
- Be a Singaporean Citizen or PR physically based in Singapore
- Minimum of 75% attendance (this means that you must attend at least 6 out of 7 lessons)
- Pass the assessment
Are there instalment plans available?
Email: contact@verticalinstitute.com
Phone: 6950 7023
How do I obtain IBF funding support? Do I need to pay the full fee first?
For Self-Sponsored:
You must be a Singaporean or Singapore Permanent Resident (PR) that is physically based in Singapore. You will only need to pay the course fees minus the funding support. For example, if you are eligible for 70% funding support, you will only be paying S$610.50 nett, which can be paid with your SkillsFuture Credits.
For Company-Sponsored:
You must be a Singaporean or Singapore Permanent Resident (PR) that is physically based in Singapore and working in an eligible company:
- Financial Institutions that are regulated by the Monetary Authority of Singapore (MAS) (either licensed / exempted from licensing)
- Fintech companies that are registered with the Singapore Fintech Association
Your company will pay the course fees minus the funding support. For example, if you are eligible for 70% funding support, the company will be paying S$610.50 nett for company-sponsored participants.
Eligible companies will further be able to claim the remaining course fees after funding with the Training Allowance Grant (TAG) (S$10/hour of eligible training and assessment hours).
Is there a Cybersecurity Certificate granted at the end of the course?
Our programmes are well-regarded by top companies, who contribute to our curriculum and use our courses to train their own teams.
Are there any pre-requisites for this course?
What softwares do I need to download?
You will need to have your own personal laptop/PC to attend the bootcamp.
What if I cannot attend a class?
Your attendance is only counted if you attend a makeup class.
What are the other in-demand courses at Vertical Institute?
- Data Analytics Course
- Digital Marketing Course
- Blockchain & Cryptocurrency Course
- UX Design Course
- Advanced Data Analytics Course
- Data Science Course
- Generative AI Course
With these resources, students have the opportunity to cultivate their tech skills and set a strong foundation for a successful career in the ever-evolving technology industry. Singaporeans and PRs are eligible for government course subsidies at Vertical Institute.
Join the Cyber Security Course Now!
Advance your career from home with Vertical Institute’s comprehensive cyber security course in Singapore. Enrol now and take the first step towards a secure and prosperous future in the cyber security field.
Book a call with our team

Other ways to reach us
Other ways to reach us
Book a call with our team